What is a Cloud Proxy?
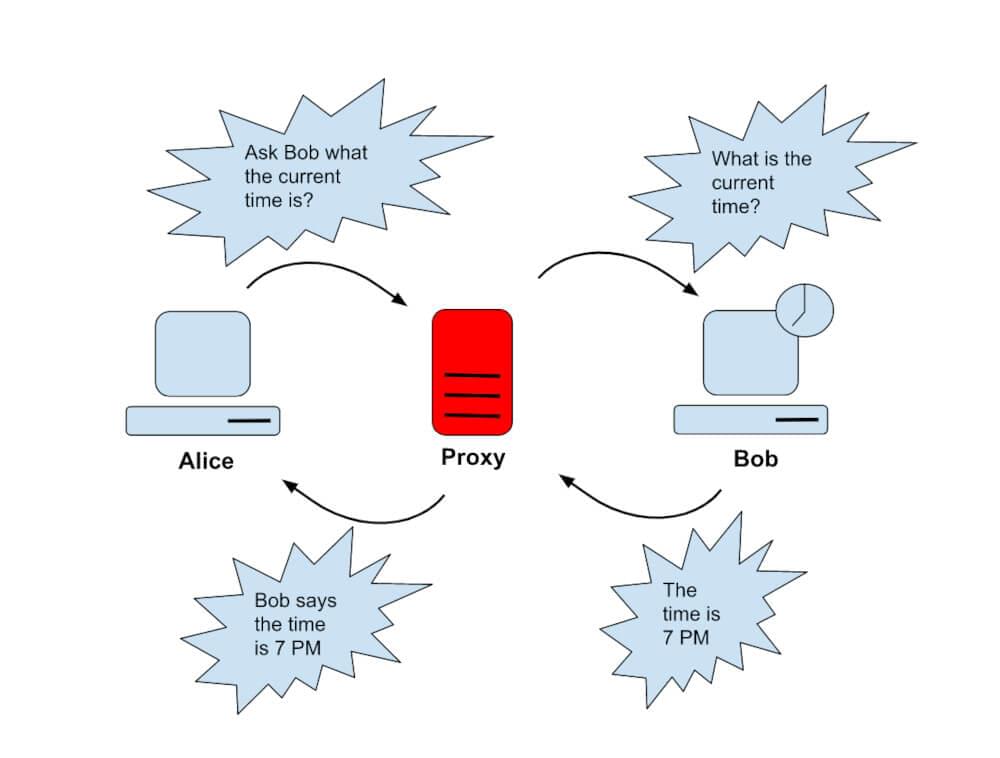
Cloud Proxy, simply put, acts as an intermediary between the internet and the client. It has a cloud server rather than a data center that works by forwarding incoming user requests to web servers for processing after verification.
Cloud is the word that has been on fire since Amazon started its web services business Have you ever tried accessing blocked web pages? That’s one of the uses of proxy servers which are much more time-efficient than on-premise data centers that require complex setups and still fail when needed which just means high maintenance costs. Cloud-based proxy is just proxy servers on the cloud.
Traditionally, data centers or on-premise servers have been used for decades, but since the cloud was discovered, everything changed. Many companies preferred the cloud because they could store scraped data on the cloud.
So what is a proxy?
A proxy’s primary function is to keep your IP address or actual location from the black hat hackers, trying to monitor your network activity, stealing sensitive data, etc. Due to their IP address, proxy servers are gateways for computers and the web. Your requests on the internet are routed to the proxy, which receives responses from the web server and forwards them to your browsers, like Chrome, Safari, Firefox, and Microsoft Edge.
Proxy servers are managed by a third party, acting as a gateway between your computer and the internet, verifying incoming requests and forwarding them to other servers for processing. Depending on the proxy type being, you may either be visible or invincible to the servers that process the proxy and your ISP but are hidden from the web servers it requests the resources from.
Cloud Proxies: How Do They Work?

Cloud-based proxy helps traffic reach an online address. Your computer is then able to receive data from the website through the proxy server. By acting as a portal between the user and the website, it works like a proxy pool. Depending on your needs, use case, or company policy, proxy servers offer varying levels of functionality, security, and privacy. The proxy is generally regarded as the safest way to inspect inline traffic compared to other methods.
You can run a cloud-based proxy server on Google Cloud or AWS or even Azure but that would just mean a lot of manual labour which is not recommended at all. Have a look at the best proxy providers for web scraping.
Cloud Proxy Servers: Why Should You Use One?

Proxies continue to be a wonderful solution for enterprises. Several things can be accomplished with the assistance of managed cloud proxies, including, but not limited to:
- Enhanced Security
- Access To Content Globally
- Activity Moderation
- Private Web Browsing
- Enhanced Performance & Bandwidth Savings
- Performance Improvement
- Avoid Server-side Crashes
- Perform Sensitive Tasks
Proxy-based Security: How Does It Work?

Proxies work in a way that can compromise data, so leading companies like Microsoft condemn using them for their customer’s privacy and cloud-based security. It would be very good to analyze if proxies are for you beforehand.
With cloud-based proxies, one needs to know the techniques utilized by the Cloud Access Security Agent/Broker or CASB and the need to use them. To ensure we know what we are talking about, SaaS does not offer security features. CASB includes the security enforcements like data encryption, logging, user authentication, and single sign-on or SSO so that the user feels secure when using the proxy.
Say a company wants to use a SaaS that doesn’t meet its security requirements. A solution that enables out-of-band connectivity is advantageous in this circumstance. The ways with which CASB adds extra security features are two. The first would be using the API suggested in SaaS to integrate additional functionalities.
Secondly, another way would be to move the app traffic through an upstream proxy so that the agent (CASB) processes the fundamental HTTP data flow directly. For those unaware of these technical terms involving proxies, it basically means that they are a go-between the client browser and SaaS, receiving requests and responses and responding when sent.
Each approach has its pros and cons. SaaS solutions are required to use API which shows that API is linked with a specific service or a set of them.
This proves that cloud-based proxy’s security might be much more versatile. However, it still needs to be customized, which can be done in a more straightforward approach because that generally works. Most SaaS applications handle HTTP, and so security can be worked around with a broad range of SaaS apps.
This level of flexibility poses threats and challenges. What happens next if the cloud-based proxy is overloaded or is not responding? If SaaS, which may not be aware that a proxy is handling their services, decides to change the distribution of their pages, make adjustments to their application, or customize in different ways and the proxy isn’t aware of it?
Microsoft has explained that proxy-based security leads to poor performance and usability.
How are these issues dealt by the SaaS provisioners when the products causing these problems are out of their control?
This technical issue has briefly been explained by Microsoft.
What Is A Proxy Number?

Proxy Number is a feature that connects your real phone number to the conversing party with a cloud proxy so that you are unidentifiable. The way this so-called Proxy Number is being applied in entire industries by having a brand-masked phone number. Let’s suppose you are a company that wants to message its customers about a promotion, it would just use a Proxy Number to mask its real number into a brand name. That way the privacy of any number behind that is maintained.
Proxy Number works in a way that it masks real phone numbers through a cloud server as an intermediary. How this works is, it let’s say you want to call an Uber driver but want to hide your identity so a virtual number would be assigned to you. This virtual number is used to route your call through the cloud proxy, which switches your real phone number to a virtual number. Proxy Numbers can also be used to call over the internet, also called Voice over Internet Protocol (VoIP).
There are multiple uses of a Proxy Number. However, we can consider a scenario here. For example, you can use Proxy Number to record and transcribe calls for your business to analyze communications with the customer and improve the overall customer experience through that.
Advantages of Proxy Cloud Servers
The primary purpose of cloud proxy servers has been to mask the IP addresses of the clients. This is a very effective way of preventing any hacker from accessing your computer by preventing them from doing so.
Apart from masking your IP, it gives additional protected layer by connecting through the server.
- Websites unblocked
Many website owners restrict the content on their websites to some geographical regions, primarily due to the country’s copyright law. Those contents will not be available to individuals outside of those regions, so they will not be able to access them. Some organizations and ISPs also restrict access to certain websites by imposing restrictions. It is also possible to bypass these restrictions by using a proxy server. Since the IP address is hidden when you use a proxy, you can access geo-restricted sites regardless of where you are on the globe. - Maintaining anonymity
When they try to access your computer, they will be logged into a proxy rather than the computer’s actual IP address while trying to access your computer. Moreover, since you will be hiding your IP address, the websites will not be able to track you because you will not be identifiable. Using a proxy server, the user can remain anonymous due to the proxy. - Assistive technology
Some proxy servers use cache data for their operations. These proxies are designed to store all of the necessary information once a user visits a website, and they do this through the cache data. Consequently, if a user visits the same page more than once on the same computer, the page will display faster. However, it is essential to note that this is only possible if the proxy has the necessary cache data from the website. As a result, it needs to request the information from the remote server if it doesn’t already have it. If you are in this situation, you may not notice any differences in the loading times of the pages. - Providing protection
Whenever you are browsing the internet, there is an excellent chance that you may end up visiting malicious websites. Should you see such a site, there is a possibility that malware will sneak onto your system and cause irreversible damage. In the same way, many unreliable websites have been set up by hackers. Your personal information will be at risk if you access one of them. Proxy servers prevent your system from making direct requests to those sites. The proxy end will inevitably be exposed to the threats posed by such websites. In this way, your system can remain as protected as possible.
Disadvantages of Cloud Proxy Servers
- Cloud Proxy Servers Lack of Security
Anonymous proxy is of great advantage, but they lack the encryption aspect. It is common for most proxies to encrypt their data with SSL certificates to protect their users’ privacy. I want to point out that it is essential to keep in mind that, for the time being, this is not enough to protect us from the types of attacks that we are experiencing today. SSL type encryption will make data less secure if it is used to encrypt data traveling through the server. There are particular threats to the security of SSL encryption, namely SSL stripping, which is designed to bypass the encryption of SSL protocol. - Monitoring Personal Information
You may lose access to all your personal information if proxy cloud servers use cache data to remember your passwords. This won’t be a problem, as long as nobody from outside gathers them. On the other hand, there is a possibility that the proxy itself may cause the problem. Even though employees are working under a representative, there is still a potential for them to misuse this information. Therefore, purchasing a proxy from a legitimate provider is always recommended to enjoy a secure connection. - Expensive
In addition to being expensive, managing cloud based proxy can be difficult. It will be difficult for small businesses to cover this expense, even though large organizations can easily afford it. Several other costs are involved in this process, including installation.
Crawlbase’s Smart Proxy allows you to be highly efficient and secure at cloud proxies at affordable pricing without having to manage a ton of things at an infrastructure level. Instead, it allows you to focus on your use case and how you can expand your operations or successfully meet your requirements without hassle. - Compatibility issues
Your local network may not always be compatible with a cloud proxy. It is important to note that both the cloud proxy and the web have their configurations. You either have to configure them or use a cloud proxy that fully matches your network if you want to use a proxy cloud server this way.